PENETRATION TESTING FOR SMALL & MID-SIZED TEAMS
See how attackers would actually break into your Network
Start with a focused external network penetration test (1–10 IPs) and add internal, app, or cloud testing as needed.
External Network Penetration Test (1-10 IPs)
The starting point for most small and mid‑sized teams.
What we test
- Up to 10 externally facing IP addresses
- Internet‑reachable services like VPNs, remote access gateways, firewalls, and exposed web interfaces
- Realistic exploitation attempts against meaningful findings (not just scanner output)
What you get
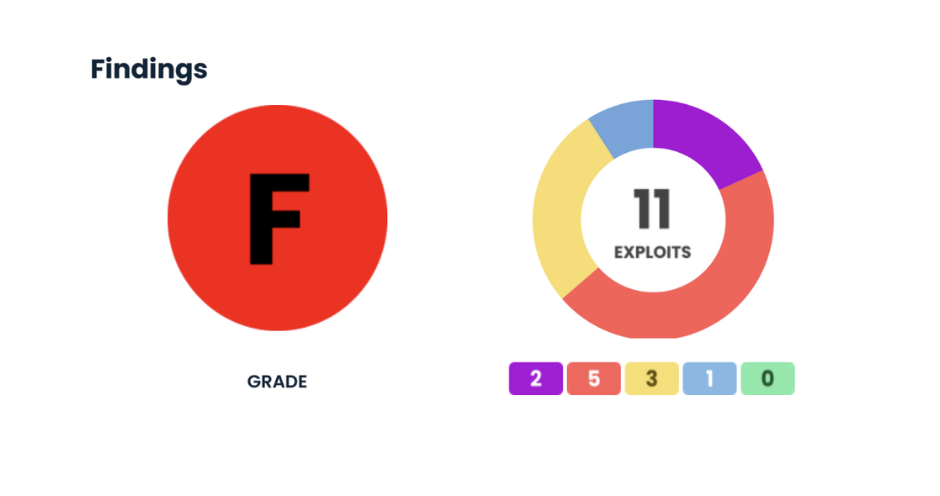
- Executive summary in plain English: what we did, what we found, and how bad it is
- Technical report with evidence, impact, and step‑by‑step remediation guidance
- Risk‑ranked fix list (what to do in the next 30, 60, 90 days)
- Live read‑out session with time for your questions
Pricing
- External network penetration test (up to 10 IPs)
- From $5,000 per engagement
- Fixed‑fee pricing for the agreed scope, with no surprise hourly bills unless you approve changes.
Note for existing customers
Shadowbear Cyber Defense Suite – Command Defense clients receive one scoped external test (up to 10 IPs) per 12‑month term included in their plan.
Other penetration tests we offer
External is where most customers start. When you’re ready, we can go deeper.
Internal penetration testing
Simulates an attacker or malicious insider who’s already on your internal network (e.g., after a phishing attack or stolen laptop).
Web application & API testing
Focused tests against specific apps or APIs you build or host, looking for auth issues, injection, access control problems, and data exposure.
Cloud Penetration Testing
Cloud assets could include virtual
machines, databases, storage
buckets, or any critical cloud
services you use.
How a penetration test with Shadowbear works
Scoping call (30 minutes)
We clarify your goals (compliance, customer requirement, internal assurance), pick the right test type (usually external first), and agree on targets and out‑of‑scope systems.
Rules of engagement & schedule
We set testing windows, notification rules, and any constraints (e.g., no production data tampering), then lock the calendar.
Testing & validation
We perform the agreed test within the window, validate real‑world exploitable issues, and alert you immediately if we see anything that needs urgent attention.
Report & debrief
You get an executive summary and detailed technical report, then we walk you through what we found, what we tried, and what to fix in what order.
FAQs
Do I need a full penetration test, or just an external one?
Most small and mid‑sized organizations start with an external penetration test. It shows how exposed you are from the internet and gives you a clear starting point. Internal, app, and cloud tests are typically added once you’ve addressed the external surface or have specific requirements.
What’s the difference between a pen test and a vulnerability scan?
Scans list potential issues. A penetration test is a human trying to turn those issues into real attack paths. If you need to prove to a customer, auditor, or yourself that someone has tried to break in and you fixed what they found, you want a pen test.
How does this relate to the Cyber Defense Suite?
The Cyber Defense Suite is ongoing protection: monitoring, training, hardening, backup, and incident response. Pen tests are point‑in‑time attacks that validate and improve what your ongoing defenses are doing. Many clients combine an annual pen test with the Cyber Defense Suite.
Will testing disrupt our systems?
Our standard external tests are designed not to impact production. We coordinate timing and throttle testing where needed. If you want more aggressive internal or app testing, we’ll build that into the rules of engagement.
Will this satisfy my compliance or customer pen test requirement?
In most cases, yes. Our reports include scope, methods, findings, and remediation status, the things auditors and customers expect. If you have a specific requirement (e.g., wording in a contract), we’ll review it during the scoping call.


